Cardinal Pill Testing
Overview
Malware analysis relies heavily on the use of
virtual machines for functionality and for safety. There are subtle
differences in operation between virtual machines and physical
machines. Contemporary malware checks for these differences to detect
that it is being analyzed, and may abort or modify its behavior.
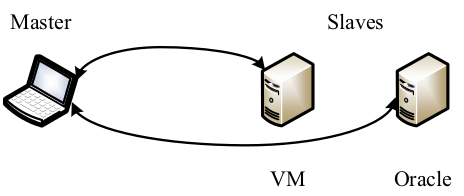
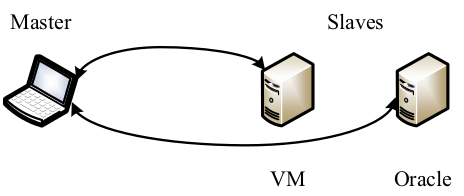
Testing Architecture
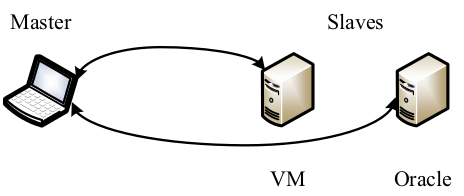
- Master
- The master issues commands to a slave to run each test case.
- At certain points, the test case in a slave will notify the master
to save system states.
- Slave
- The VM slave is running a system virtual machine, while the Oracle
slave provides a reference.
- Both of them store the same set of test cases locally.
- In addition to the test cases, there is a daemon process inside
each slave which receives the command from the master.
Software & Code
- System Virtual Machines
- Generally, our architecture can test any system virtual machines
that support serial debugging, such as QEMU, VMware, Bochs, etc.
- The host system can be any OS but the guest system is limited to
Windows now. Extension to other guest systems requires moderate
engineering work but no hurdles in theory.
- QEMU,
Bochs,
Ether
- Master Scripts
- main.wds This is the main loop used by the
Master. WinDbg 6.12 is required.
- SaveStates.wds This script helps
Master save slave states to local disk. Python 2.7 is required.
- Write.py Used by SaveStates.wds.
- Reboot.wds Reboot the slave.
- Slave
- Test Cases (Please use MASM for compilation and linking).
- Pills (Pills found in our evaluation).
- Daemon (Please use VS for compilation and linking).
- Usage
- Compile test cases and put them in slave Windows.
- Put the daemon in slave Windows and set up the root dir of test
cases in its code. Make daemon bootable at system startup.
- Run main.wds in the Master.
- System States for each test case will stored in the Master. After
all test cases are executed, you can compare them.
Appendix
- QEMU failed to set mxcsr flags
- 'Invalid Operation Flag', 'Denormal Flag', 'Precision Flag', 'Overflow Flag', 'Underflow Flag', 'Divide-by-Zero Flag', 'resv', 'Flush to Zero', 'Rounding Control Precision Mask1', 'Rounding Control Precision Mask0', 'Denormals Are Zeros', 'Precision Mask', 'Underflow Mask', 'Overflow Mask', 'Divide-by-Zero Mask', 'Denormal Operation Mask', 'Invalid Operation Mask'
- QEMU failed to raise exception
- 0xC00002B5: STATUS_FLOAT_MULTIPLE_TRAPS
- 0xC00002B4: STATUS_FLOAT_MULTIPLE_FAULTS
- 0xC0000005: STATUS_ACCESS_VIOLATION
- 0xC000001E: STATUS_INVALID_LOCK_SEQUENCE
- 0xC0000096: STATUS_PRIVILEGED_INSTRUCTION
- QEMU failed to set floating-point registers correclty
- fptw (oracle|qemu)
'Zero|Special', 'Special|Zero', 'Empty|Zero', 'Special|Empty', 'Special|Valid', 'Zero|Empty'
- fpsw
'Stack fault', 'Invalid Operation', 'Condition Code', 'Zero Divide', 'FPU Busy', 'Error Summary Status', 'Top of Stack Pointer'
Acknowledgments
This material is based upon work supported by the Department of Homeland Security, and Space and Naval Warfare Systems Center, San Diego, under Contract No. N66001-10-C-2018. Any opinions, findings, and conclusions or recommendations expressed in this material are those of the author(s) and do not necessarily reflect the views of the Department of Homeland Security for the Space and Naval Warfare Systems Center, San Diego.
Links